06 Jan How to Detect Spyware on a Mac
Please read this whole guide before doing anything.
Only follow these instructions if you have already scanned your Mac with Macware Spyware Cleaner.
The following procedure will help identify whether your system has been modified. Don’t be alarmed by the complexity of these instructions — they’re easy to carry out and won’t change anything on your Mac.
These steps are to be taken while booted in “normal” mode, not in safe mode. If you’re now running in safe mode, reboot as usual before continuing.
Below are instructions to enter some UNIX shell commands. The commands are harmless, but they must be entered exactly as given in order to work. After you have executed each command copy/paste the result into a text file.
Some of the commands will line-wrap or scroll in your browser, but each one is really just a single line, all of which must be selected. You can accomplish this easily by triple-clicking anywhere in the line. The whole line will highlight, and you can then either copy or drag it.
Note: If you have more than one user account, Step 2 must be taken as an administrator. Ordinarily that would be the user created automatically when you booted the system for the first time. The other steps should be taken as the user who has the problem, if different. Most personal Macs have only one user, and in that case this paragraph doesn’t apply.
Launch the Terminal application in any of the following ways:
☞ Enter the first few letters of its name into a Spotlight search. Select it in the results (it should be at the top.)
☞ In the Finder, select Go ▹ Utilities from the menu bar, or press the key combination shift-command-U. The application is in the folder that opens.
☞ Open LaunchPad. Click Utilities, then Terminal in the page that opens.
When you launch Terminal, a text window will open with a line already in it, ending either in a dollar sign (“$”) or a percent sign (“%”). If you get the percent sign, enter “sh” and press return. You should then get a new line ending in a dollar sign.
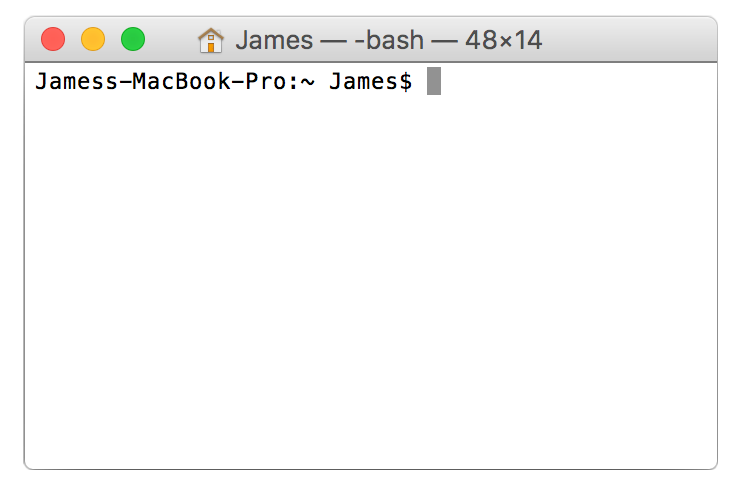
Terminal Command Prompt
Step 1
Copy or drag — do not type — the line below into the Terminal window, then press return:
kextstat -kl | awk '!/com\.apple/{printf "%s %s\n", $6, $7}'
Post the lines of output (if any) that appear below what you just entered (the text, please, not a screenshot.) You can omit the final line ending in “$”.
Step 2
Repeat with this line:
sudo launchctl list | sed 1d | awk '!/0x|com\.(apple|openssh|vix)|edu\.mit|org\.(amavis|apache|cups|isc|ntp|postfix|x)/{print $3}'
This time, you’ll be prompted for your login password, which won’t be displayed when you type it. You may get a one-time warning not to screw up. You don’t need to post the warning.
Note: If you don’t have a login password, you’ll need to set one before taking this step. If that’s not possible, skip to the next step.
Step 3
launchctl list | sed 1d | awk '!/0x|com\.apple|edu\.mit|org\.(x|openbsd)/{print $3}'
Step 4
ls -1A /e*/mach* {,/}L*/{Ad,Compon,Ex,Fram,In,Keyb,La,Mail/Bu,P*P,Priv,Qu,Scripti,Servi,Spo,Sta}* L*/Fonts 2> /dev/null
Step 5
osascript -e 'tell application "System Events" to get name of every login item' 2> /dev/null
Remember, steps 1-5 are all drag-and-drop or copy-and-paste, whichever you prefer — no typing, except your password. Also remember to paste the output into a text file.
You can then quit Terminal.
Step 6
Post your results here;
Our staff will review the results as soon as possible and inform you of any potential spyware found.
